Data Center Audit Report Template. Redundant fiber optic connectivity is the gold standard for data centers. But IT leaders still should manage external and internal dangers to keep away from downtime, which can result in losing millions of dollars a day. Business days, and shall course of measures to protect forensic proof and remove the cause of the Data Breach. For smaller project movements, guaranteeing that users are capable of proceed to do their jobs – training, checking the technical capabilities of the new system and so forth – may be all that’s required.
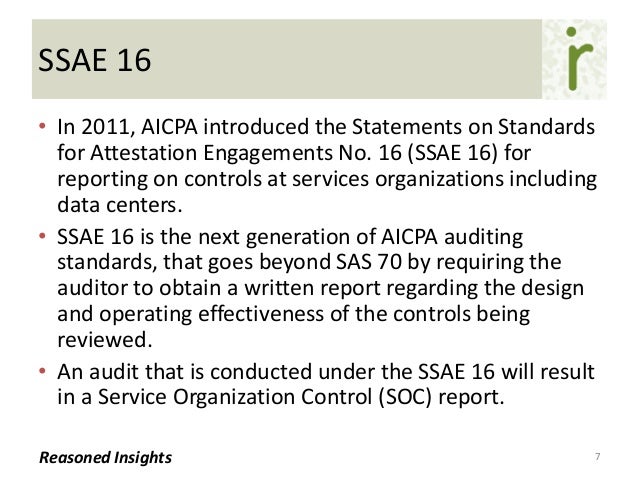
First, you have to understand the differing types ofSOC 2 reportsto determine what you need right now. At a granular level, this implies operating scripts sometimes to pull an inventory of all software program installed, hardware devices, firmware versions, and drivers. Smart CIOs treat data centers as capital belongings, with their very own budgeting, management goals and periodic upgrade requirements.
Our consultants determine stakeholders and sponsors inside the business to reply questions, guarantee essential help and supply access to assets. Keep in mind, a improve can’t be led if there isn’t a majority, for instance in the matter that the bottom number of participants to implement the accretion is absent. Intermediate relays replace hyperlink encapsulation at each hop, and examine the IP layer for routing functions. Submitted reports will mechanically be saved as PDFs which are simple to obtain, share, and print. Here’s what must occur after the hole analysis to place these good ideas into action.
The new alternatives past the plan evaluation stress checks the kid maintenance aligned place of the arrangement to guarantee that you’ve got got entered take forward charges which might be reasonable. It moreover shows a unquestionable earn put as a lot as the native investment laboratory analysis just as different important financial pointers and markers gone affordable allowance projections.

This means that your initial detection staff may solely have a couple of hours to begin the escalation process in order that your organization can investigate, decide the complete diploma of breach, and begin notifications. One of your servers all of a sudden went offline, inflicting a major outage. Looking at the logs, you see “root logged on” “root initiated a shutdown”.
Step 1: Choose A Framework That Helps Arrange Your Plans
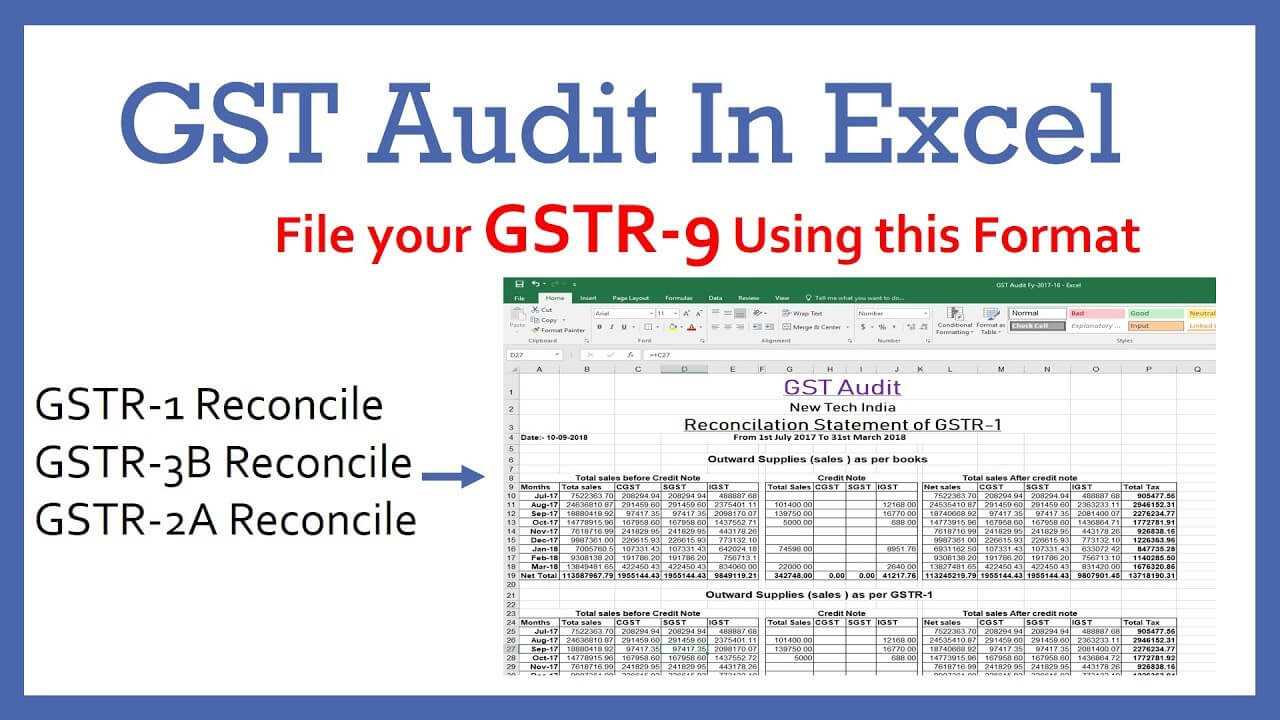
It does not matter should you need Excel templates for budgeting the subsequent fiscal yr, monitoring your business inventory, planning out meals, or creating a fantasy football draft sheet, there are lots of Microsoft Excel templates for you. Our ITIL-compliant reference process mannequin contains 102 officially licensed checklists, and the most popular ITIL templates can be found for obtain here in our ITIL Wiki. A formal process used to make certain that modifications to a system are introduced in a controlled and coordinated manner.
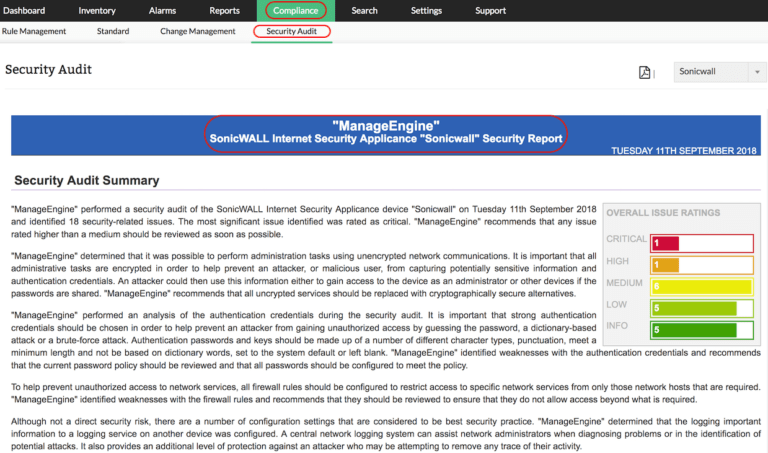
Of course, information centers or the IT infrastructure itself doesn’t function in isolation. Spending money on information middle danger administration might not essentially be a prime precedence for all managers – most departmental goals pale compared to meeting revenue targets. For organizations that must comply with legal, contractual, or regulatory necessities, periodic information heart danger assessments and disaster testing are inevitable.
Description And Design
Click via the picture gallery above to see extra of the premium annual report magazine template. • Additional measures such as mantraps – consisting of two separate doors with an airlock in between – perform to ensure that just one door to the info heart could be opened at a time – with authentication required for both doorways.
For example, the most effective follow response to a workstation contaminated with malware is to re-image the workstation entirely. This removes the risk of a latent infection, nevertheless it also erases logs and usage historical past which might assist determine the place the malware came from.

Consider itemizing all the most important parts that your annual report should embody. Having a solid outline will assist you to write with function, quite than rambling on. Don’t neglect to add charts, graphs, and numerous infographic components to your annual report.
Report Sorts
An evaluation report may be explained as a doc having a comprehensive abstract of the results of your analysis concerning a specific subject, project, problem, or state of affairs and… Menu Compliance Audit ReportMenu Compliance Audit Report Sample offers you an effective approach to report your findings each time you perform menu compliance auditing. With Menu Compliance Audit Report PDF Template, health inspectors can easily create custom-made PDF reviews.

Video cameras and doorways with access management would possibly lose their connection to the central system too. Luckily, many pure disasters may be forecasted, and subsequently, prepared for.
Make sure you’ve allotted sufficient resources to finishing up the plan—and communicated it to everybody in your organization. Goal—In Step 2 of the hole analysis, you identified the place you’d like to be when it comes to efficiency. Instead, they could say they wish their soup kitchen was serving 25,000 meals right now as an alternative of 10,000 meals.
• Constant surveillance of a data center is important for monitoring daily operations. In order to ensure that all areas are functioning correctly and that each element of the constructing is secure and guarded at all times, surveillance tools should be installed all through the building at each entrance, exit, and access level.

Maternal and Infant Health Mapping ToolMap and mix county-level datasets on maternal health, infant health, and well being resources. Be prepared with media and license keys for installing backup server client software program if needed.

This reduces the possibility that pointless adjustments might be launched to a system, that faults or vulnerabilities are introduced to the system, or that changes made by other users are undone. Ensure that your backup and construct servers are able to go in the new data middle prior to the relocation date.

The three applications mentioned above are merely the tip of the iceberg when you’re speaking in regards to the power and flexibility of dynamic digital data reviews. This first IT report template deals with technical issue administration and is very useful for IT leaders.
However, this isn’t always the case, as any model injury in the eyes of individuals with an opposing opinion to that presented by the group may sometimes be outweighed by strengthening the brand within the eyes of others. Furthermore, if an organization or individual gives in to demands that others perceive as wrong-headed, that can then provoke a counter-backlash. Educational materials at all ranges from pre-school to post-doctoral is available from websites.

The native technician talks to the workstation proprietor, picks it up, verifies that critical data has been saved, and re-installs the usual firm build on it. The workstation is returned to the proprietor and the ticket is closed.
PCI DSS GUIDE’s goal is to clarify the method of PCI DSS compliance in addition to to supply some frequent sense for that course of and to help individuals preserve their security while they transfer via their compliance processes. Inspect all sign and information cables on servers and network units to make sure they are not subject to interference or touch. Implement controls to adequately prevent floods and other disasters from affecting the information center.

In the coming months, OCR will notify the chosen covered entities in writing by way of e-mail about their selection for a desk audit. The OCR notification letter will introduce the audit team, clarify the audit course of and talk about OCR’s expectations in additional element.
Internet usage by cell and pill gadgets exceeded desktop worldwide for the primary time in October 2016. Access to the ARPANET was expanded in 1981 when the National Science Foundation funded the Computer Science Network .

ISACA® is totally tooled and prepared to raise your personal or enterprise data and skills base. A SOC audit will allow you to higher perceive the current efficiency of your security controls and spot potential issues. This gives you a chance to fix them earlier than they start snowballing.

Get the newest articles on startup safety and compliance finest practices delivered straight to your inbox. As we mentioned earlier, the AICPA doesn’t provide clear pointers concerning the controls you must have in place to be SOC 2 compliant. Finally, privacy refers again to the protection and anonymity of person information.
Do you may have a Disaster Recovery site with this knowledge being replicated by a storage array or cluster product? Regardless, know and take a look at how you would restore the information within the new information center should issues go awry.

Likewise our COBIT® certificates show your understanding and ability to implement the main international framework for enterprise governance of knowledge and expertise . Beyond certificates, ISACA additionally offers globally acknowledged CISA®, CRISC™, CISM®, CGEIT® and CSX-P certifications that affirm holders to be among the most qualified data methods and cybersecurity professionals on the planet. As an ISACA member, you could have access to a network of dynamic info systems professionals near at hand by way of our greater than 200 local chapters, and around the globe by way of our over a hundred sixty five,000-strong global membership neighborhood.
The latest innovations in data migration best-practices and technologies. Please note that this listing isn’t exhaustive, there are numerous more actions that might be added here however it should offer you an inexpensive start line. Hope for the most effective however plan for the worst case scenario which is an failed migration.

Check your capability to communicate with internal escalations, external escalations, and end-users. If you are not cautious, your test restore could overwrite your real server, or it may disrupt companies by placing a second, conflicting, server on the community. Choose your recovery goal fastidiously and isolate the restored server by disconnecting the community.

In theLabelfield, sort “status-update” and select it from the search outcomes. Editthe Page Properties macro and enter aPage Properties IDfor this macro; in this instance we’ll use status-update-design. This will enable us to report on the standing of just the Design group in a while.

The word is usually nonetheless capitalized to distinguish the global web from smaller networks, though many publications, together with the AP Stylebook since 2016, recommend the lowercase type in each case. In 2016, the Oxford English Dictionary discovered that, primarily based on a research of round 2.5 billion printed and online sources, “Internet” was capitalized in 54% of circumstances.
It is more robust than Tier 1 in phrases of the hardware, and offers users a customizable balance between cost administration and performance. So, organizations need the right tools and processes to watch every moving a half of the info middle and deal with any dangers that come up at any point in time, including malicious cyberattacks. Big data and analytics are instrumental in forming an accurate and complete assessment of the dangers to varied operations that the information heart permits, such as knowledge entry, application mobility, and DevOps.

Generally, OCR will use the audit reviews to determine what kinds of technical help must be developed and what forms of corrective motion could be most helpful. Through the data gleaned from the audits, OCR will develop tools and guidance to help the industry in compliance self-evaluation and in stopping breaches.
It is a good way to visible your knowledge and present where your group is struggling and thriving. In our dialogue around the hole evaluation template under, we’ll discuss particularly about how a niche analysis can be utilized inside a division; it may also be used for your complete enterprise or for a single course of. The 4 steps outlined within the template beneath will help ensure you realize precisely what issues you’re going through and tips on how to go about fixing them.
[ssba-buttons]